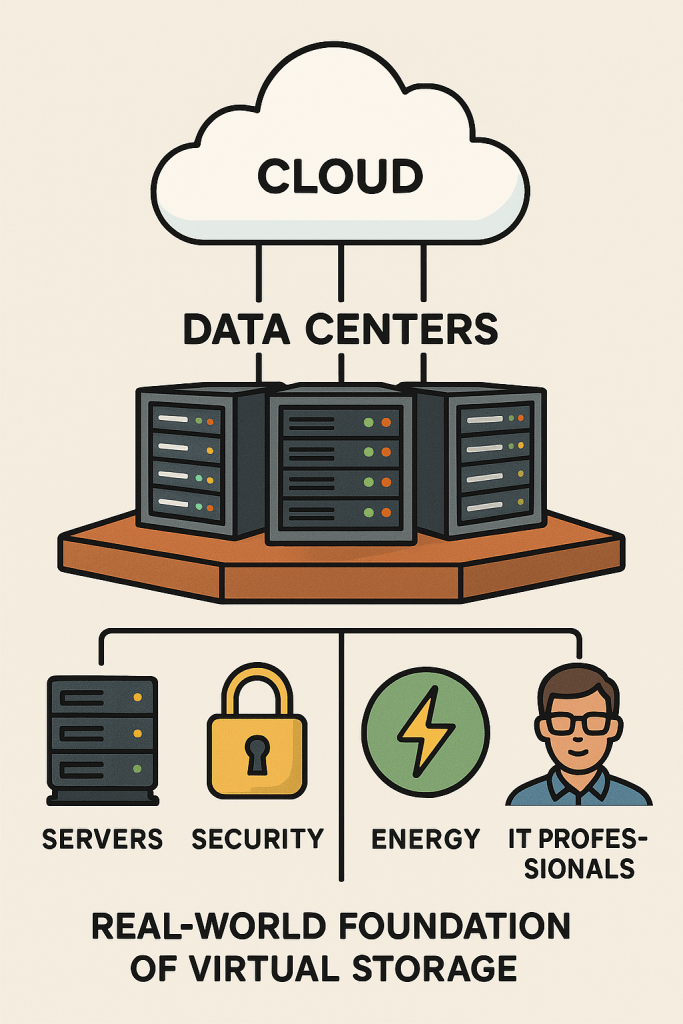
CLOUD STORAGE ISN’T ACTUALLY IN THE SKY — IT’S A MARKETING TERM. WHEN YOU STORE FILES “IN THE CLOUD,” YOU’RE REALLY STORING THEM ON PHYSICAL SERVERS HOUSED IN DATA CENTERS AROUND THE WORLD. THESE SERVERS ARE OWNED AND MAINTAINED BY COMPANIES LIKE AMAZON, MICROSOFT, AND GOOGLE. YOU ACCESS YOUR DATA OVER THE INTERNET, WHICH GIVES THE ILLUSION THAT IT’S FLOATING IN THE CLOUD, BUT IN REALITY, IT’S SAFELY STORED ON EARTH IN HIGHLY SECURE, CLIMATE-CONTROLLED FACILITIES.
Why Is Cloud Storage Not Really in the Clouds?
Explore the truth behind cloud storage—why it’s not free, how it works, and what you’re actually paying for. A deep, inspiring dive from the Rise & Inspire perspective.
What Powers the Cloud? A Deep Dive into the Reality of Cloud Storage
By Johnbritto Kurusumuthu
Founder & Editor-in-Chief, Rise & Inspire
Introduction: A Cloud You Can’t Touch, But Can’t Do Without
In our digitally driven world, “the cloud” has become an everyday term. From uploading photos to syncing documents across devices, cloud storage feels like magic—limitless, weightless, and always there. But the deeper truth is that cloud computing is not an abstraction; it’s an architectural marvel built on vast physical systems, human expertise, and continuous innovation.
This blog post—part research paper, part reflective insight—explores what cloud storage really is, why it costs money, and whether it can ever be truly free. As always, we examine it through the Rise & Inspire lens: with clarity, purpose, and a commitment to empowering minds in a rapidly evolving world.
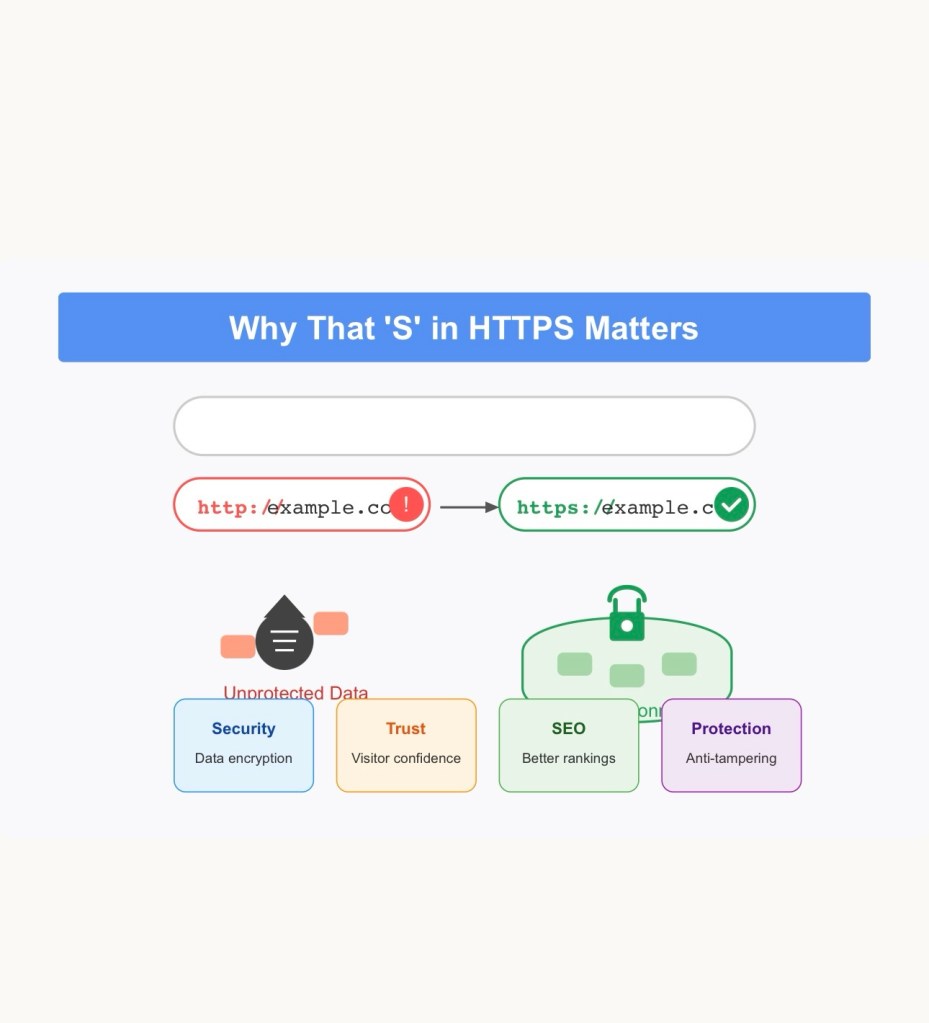
1. Understanding the Cloud: More Than a Metaphor
At a basic level, the cloud in technology refers to a global network of servers that allow you to store, manage, and process data remotely, rather than on your local device.
Rather than saving files to a hard drive or USB stick, cloud computing enables data to reside on remote servers, accessible via the internet. These servers are hosted in data centers across the world—secured, climate-controlled, and monitored 24/7.
Key Insight: Cloud storage is not stored in the sky—it’s stored in warehouses full of servers, powered by electricity, protected by cybersecurity protocols, and connected through high-speed fiber-optic cables.
2. Types of Cloud Storage: A Quick Technical Overview
There are three primary models of cloud storage:
Public Cloud: Owned and operated by third-party providers like Google Cloud, Amazon Web Services (AWS), and Microsoft Azure.
Private Cloud: Used by a single organisation. Offers greater control and security.
Hybrid Cloud: A combination of public and private, used for flexibility and scalability.
Popular services include:
• Google Drive
• Apple iCloud
• Dropbox
• Microsoft OneDrive
• Amazon S3
Each offers a blend of convenience, collaboration tools, and data recovery capabilities—services that are no longer luxuries, but digital necessities.
3. Why Do We Pay for Cloud Storage?
On the surface, data seems weightless. But behind every gigabyte you upload lies a massive operational effort.
a) Infrastructure Costs
Cloud providers invest billions in data centres, energy consumption, networking equipment, backup generators, and hardware upgrades.
b) Security & Maintenance
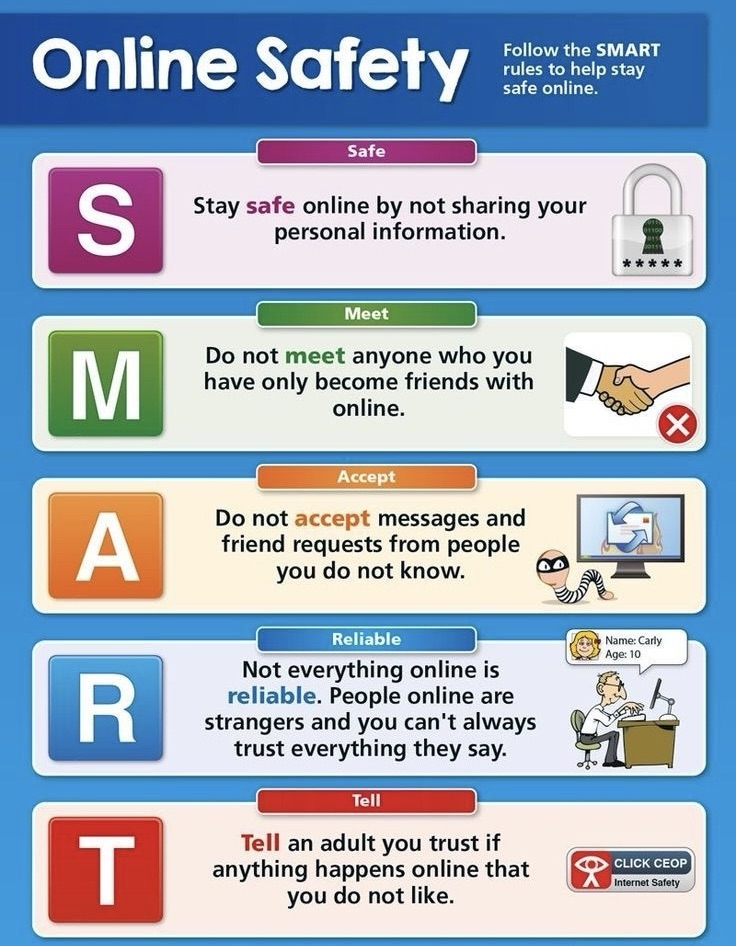
Protecting your data from breaches and cyberattacks involves advanced encryption, firewalls, and dedicated IT teams working around the clock.
c) Data Redundancy & Backup
To prevent data loss, cloud systems duplicate your files across multiple servers in different locations. This redundancy ensures resilience—but requires more storage space.
d) Scalability & Uptime
Cloud services are expected to be available 24/7. This demands load balancing, server orchestration, and real-time monitoring, all of which incur significant costs.
Fact Check: Google spends over $10 billion per year on its global data infrastructure. AWS and Microsoft are not far behind. Offering “free” services indefinitely is neither feasible nor responsible at scale.
4. The Freemium Model: Why Some Cloud Storage Is Free
Many providers offer free basic plans to attract users:
• Google Drive – 15 GB free
• Dropbox – 2 GB free
• iCloud – 5 GB free
• OneDrive – 5 GB free
This freemium model is a strategic decision: users get hooked on the convenience, and when they outgrow the free limit, they often opt for paid upgrades. The free tier is also supported by:
Advertising revenue
Cross-subsidies from other services
Data usage insights (within privacy limits)
Still, unlimited and truly free cloud storage is not viable unless funded by another commercial engine.
5. Can Cloud Storage Ever Be Completely Free?
Technically, no—not unless someone else foots the bill. Even “free” decentralised models (like some blockchain-based storage systems) require infrastructure, tokens, or peer-to-peer exchanges of storage resources.
Only two scenarios make truly free cloud storage possible:
1. It is ad-supported or subsidised by other paid services
2. It is part of a social/public infrastructure (like a government digital mission)
But such models still have costs; they are just not paid directly by the user.
6. The Bigger Picture: Why Cloud Storage Reflects the New Digital Responsibility
We are no longer storing only files. We are preserving memories, collaborating across continents, securing identities, and scaling businesses in the cloud.
This shift demands digital mindfulness:
• Know where your data lives
• Be intentional about digital clutter
• Support ethical tech infrastructure
• Understand your digital carbon footprint
When we value convenience, we must also appreciate the invisible architecture that sustains it.
7. The Rise & Inspire Perspective: Empowered, Informed, and Elevated
At Rise & Inspire, we believe knowledge must not just inform—it must elevate. Understanding the cloud reminds us that behind every seamless experience is a system of real human effort, material investment, and constant innovation.
Rather than taking the cloud for granted, we are invited to:
• Use it wisely
• Pay where due
• Protect our data
• Honour the digital ecosystem we depend on
After all, even in the sky, every cloud has a structure. And every structure deserves recognition.
Key Takeaway
Cloud storage feels free, but is sustained by complex and costly systems. Understanding this empowers us to use it responsibly and with gratitude.
More insights await. Explore the archive for clarity, strategy, and growth.
Categories: Tech Insights | Personal Development | Wake-Up Calls | Motivational Blogs
© 2025 Rise & Inspire. All Rights Reserved.
Word count:996